While the Health Insurance Portability and Accountability Act (HIPAA) was enacted in 1996 and is more than 20 years old, many businesses still struggle with compliance. The HIPAA has clear guidance on the requirements for controlling access to electronically protected health information. To comply with HIPAA, organizations need to adopt a best-practice driven approach towards data encryption and secure their data.
Healthcare has gone digital. Today, both providers and patients use a lot of apps and equipment like electronic health records (EHR), wellness apps, wearable devices etc., that collect personal data of the patients and this data is then transferred across various systems. Similarly, health payors provide access to data on claims and care management. While this has brought efficiency in patient care and improved treatment outcomes, there are potential security risks.
The data collected on various apps and systems need to be protected against hacking and unauthorized access to ensure the privacy of the patients. In 2002, ‘Privacy Rules’ were added to HIPAA to provide guidelines and security controls on sharing of protected health information such as patient names, genetic data and social security numbers etc. The rules apply to covered entities including health care providers, health plans, and health care clearing houses that electronically transmit health information.
Not following the HIPAA can be expensive to healthcare organizations. In 2018, the MD Anderson Cancer Center of the University of Texas received a $4.3 million penalty for violating the act. A laptop containing 30,000 patient records was stolen from an employee’s home. There were also two separate instances of data loss via misplaced USB drives.
HIPAA Encryption Requirements
The HIPAA encryption requirements are somewhat vague. The Act doesn’t require you to mandatorily use encryption to safeguard Protected Health Information (PHI). The 45 CFR § 164.312 of HIPAA talks about technical safeguards.
According to this, encryption and decryption are mentioned in the implementation specifications. However, the encryption and decryption implementation are “addressable” which means that it must be implemented if the covered entity after risk assessment finds that it is necessary. If the entity doesn’t find it reasonable to implement encryption, then it is required to document the reasons behind it and can implement an alternative data protection measure.
So, encryption is not mandatory in HIPAA. However, data encryption is one of the popular and effective technique to safeguard any data.
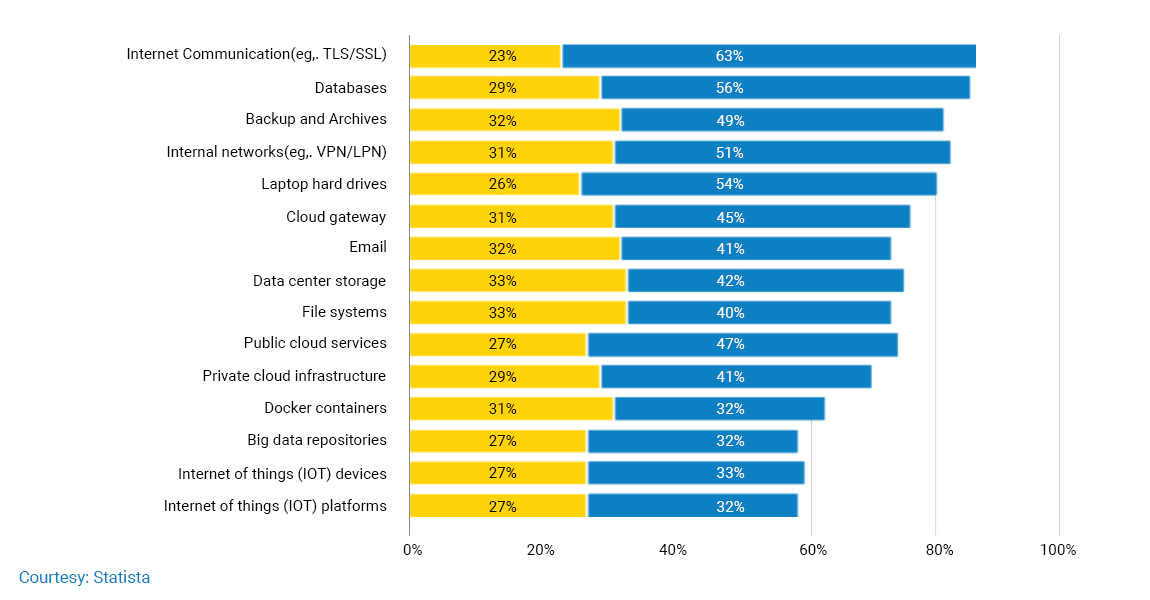
Although it is not mandatory, businesses of all types use encryption to protect their data. The following graphic by Statista, shows the worldwide usage of encryption technologies in enterprises as of FY2019.
Training Programs and Tech Solutions
As a technology partner to one of the leading medical schools in the US, we have developed engaging, useful and convenient e-learning material on HIPAA guidelines and security rule that allows covered entities to employ new technologies that can improve the quality and efficiency of patient care without any data breach.
We have helped our customers to put in place adequate policies and procedures to protect the ePHI that is created, stored or transmitted through their systems.
Our experts have conducted several training programs for healthcare professionals to create awareness and understanding of HIPAA. Our programs have helped the covered entities to implement administrative, technical and physical safeguards to ensure the confidentiality, integrity and availability of ePHI.
Gemini has also helped healthcare providers to deploy security solutions that guard against system security vulnerabilities and take measures to mitigate them.
If you need expert assistance in HIPAA encryption for your healthcare device, app or any other solution then our team will be happy to assist you. Our team of data and technology experts can help you in HIPAA compliance and securing your patient data. Click here to know more about our services.
HIPAA Encryption Best Practices
There are several best practices for managing encryption in your healthcare system or solution including.
- Centralize Your Encryption Process: Centralized management of encryption strengthens your data security by giving you full view as well as complete enforceability. A siloed process will create gaps vulnerable for theft, stolen.
- Encrypt Data that is Necessary: Your system will collect a lot of data and encryption consumes system resources like CPU time and memory which can impact the performance of your system. You don’t need to encrypt all the data as all information is not critical. So, identify the data you want to encrypt and use your system resources intelligently.
- Secure Your Encryption Keys: Encryption keys are generated to read the encrypted data. Keep it in a secured place. Don’t store keys and the data in one place.
- Control Access to Your Data: Don’t make the data accessible to everyone. Use user authentication methods like password, biometric etc., to grant access. Record info on people accessing your data.
- Periodically Assess Your Data Encryption Strategy: Assess and review your data encryption performance. Check if it is working as desired and is not putting a lot of stress on your resources.



